Our responsibility towards IT Network Security
What is Information Technology (IT)?

In a nutshell, anything related to computing technology is a component of IT.
IT in Home Computing: Some Components

Non-exhaustive list:
- Smartphones
- Tablets
- Laptops / Desktops
- Smart objects used for home automation (bulbs, doorbells, thermostats, etc.)
- Internet connection and ways to use it (WiFi, cables).
IT in Professional Computing: Some Components

Non-exhaustive list:
- All components involved in Home Computing
- Datacenters
- Servers, hypervisors, storage arrays, etc.
- Routers, switches, firewalls, etc.
- Websites, applications
- Public or private customer data
What about IT Security in Professional Computing?

IT security is the way to protect IT components against every kind of threat:
- It has to be considered as a long-term insurance.
- It must cover physical infrastructure as much as logical infrastructure.
IT Network: The Key Component to Secure?
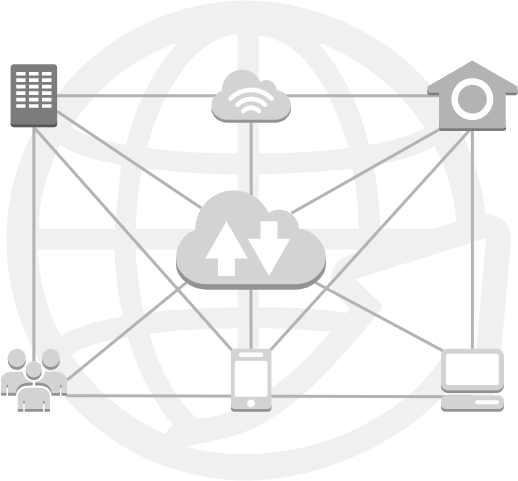
With a strong predominance of Internet-related uses, network infrastructure must be considered the backbone of computer technology.
In addition to strong reliability requirements, more and more abilities have been added to network architectures over time, such as content inspection/protection layers against cyberthreats.
Everyone Must Be Concerned About IT Network Security. Why? How?

From decision-makers to operations technicians, passing by IT Network architects, everyone should be aware of the importance of securing IT Networks.
As mentioned earlier regarding a more global scope, IT Network Security in Professional Computing must be considered a long-term insurance, which means:
- A good knowledge of the scope to protect:
- “Every fuzzy need leads to a very specific bullshit”—in less flowery language, security requires accuracy.
- Security expectations evolve over time and require adjustments regarding configuration and service contracts.
- Investment cost awareness:
- Investing in network device hardware and/or perpetual software licensing is one thing, but consider that the lifecycle policy to maintain a state-of-the-art infrastructure is about 5 years.
- Operational cost awareness:
- Typically, threat prevention features embedded in core network devices are tied to time-limited licenses. These costs are cumulative with hardware or basic software support contracts.
- In some cases, 99.99% SLA and 24/7 support is a must-have.
- The higher the security requirements, the higher the recurring costs will be.
Call to Discussion!
As you can see, this article reflects solely my opinion on this subject.
So don’t hesitate to follow my LinkedIn Feed and react to this article with your own thoughts and words!